Should I Have a Separate CamNet?
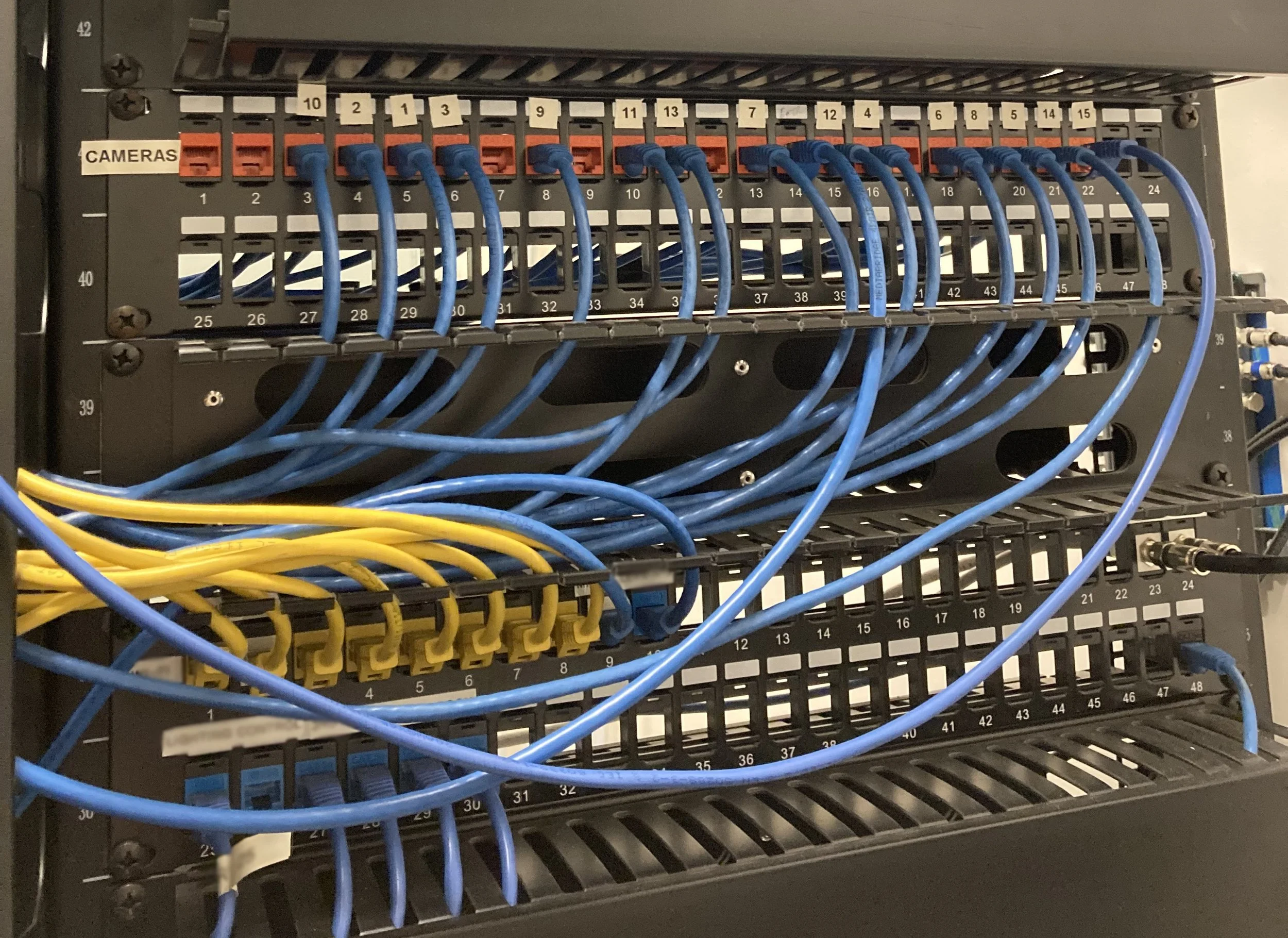
A dedicated security camera patch panel
A question we hear frequently about new installations is, “Should we have a separate camera network (or ‘camnet’) for our security equipment?” The question is especially common in mid-size facilities which are large enough to have long cabling runs and IDF cabinets*, but not a large corporate IT team with their own policy or philosophy on network management.
There are follow-up questions like “Do we need to run all that cable?” “Can we just plug them into this switch over here?”
The short answer is that Settler recommends a separate CamNet or security network where possible. It is our perspective that the benefits of keeping cameras, access controllers, and other security hardware segregated from other network equipment outweigh the costs.
PROS OF A SEPARATE CAMNET
The pros of installing a maintaining a separate camnet include:
Bandwidth Management – Security devices (especially cameras) can be bandwidth-intensive. Keeping separate routes for video data and other security communications helps ensure that security systems don’t interfere with other network traffic. And, vice versa, that regular network traffic doesn’t interrupt communications of safety-related security equipment. Video can be routed to a NAS or NVR without ever hitting the main network until incident video is needed, or in the case of a cloud system, buffered to a bridge that can be scheduled to use upload bandwidth during off-peak times.
Simplifies Troubleshooting – If/when a camera, door, alarm panel or other security device goes offline, troubleshooting can be done much faster. Security staff or contractors can troubleshoot downstream of the main network connection without waiting for network admins to troubleshoot network configurations like firewall policy or network hardware like switches. Reducing the number of teams involved makes for faster identification of the problem and faster resolution.
Sets Clear Lines of Responsibility - Keeping all security equipment on one side of a single switch or router port makes for very clear lines of responsibility. Everything from the cable termination on down is the security vendor’s responsibility. Everything from the switch or router port up to the ISP is the network administration’s responsibility. Failures on either side are clear, reducing contention over financial and operational ownership.
Reduces Cross-Compatibility Risks – While most network equipment has high degrees of interoperability thanks to well-defined global standards, not all networked security equipment is compatible with every network or every piece of networking hardware. File formats and codecs (especially if proprietary), power requirements, IP schema requirements, server rack depth, and other minutae can all cause problems when integrating security hardware into the main network. A security network that has been designed from the ground up to function as a single system provides the best shot at a smooth installation that comes online on time and on budget.
Builds System Robustness – A security network may be able to continue to function even during internet service, network, or power outages, providing ongoing access to doors, surveillance, monitoring, or other key functions. This depends on system specs, such as edge or camnet-accessible storage and backup power supplies, but if built for robustness, these systems can operate as standalone systems even if damage or outages affect the main network. Many commercial security components are also subject to high-duty cycles. Things like switches and hard drives often fail more frequently than similar non-security components. A separate network designed with high-duty-cycle security components will reduce downtime and ensure that, when downtime does occur, it does not affect the main network.
Better Cybersecurity – A camnet or security network designed in conjunction with network administrators will provide better network security than simply plugging security systems into the main network. Systems can be designed so that changes to network security policies are not required, protecting the network from outside access. Simple policies to segregate the camnet from unauthorized users reduces exposure to inadvertent or malicious access from inside the network. Changes in the surveillance environment will not trigger main network anomaly detection, reducing alert fatigue.
CONS OF A SEPARATE CAMNET
The main downside of a separate camnet is expense. Running extra cable and installing dedicated switches and drives requires a higher level of investment up front, as well as additional maintenance over time.
In general, we believe these costs are relatively minor compared to the benefits of a more secure, more robust network with plenty of bandwidth for operational and transactional communication. Although this will not be true for every implementation.
HOW TO IMPLEMENT
In small facilities with simple networks, the security system can be installed in the MDF or headroom with a direct connection to the router and downstream equipment cabled independently of the main data network.
In mid-sized facilities with IDFs, it is ideal to build a separate network for security from the MDF down. In some mid-sized facilities and almost all large facilities, duplicating backbone connections to MDFs may simply be cost prohibitive. Although network topology is outside the scope of this article, for most network types in mid/large facilities, we recommend building camera/security networks as separate trunks near the network edge, with local, on-trunk storage and power to minimize impacts to the main network. Bandwidth concerns are much smaller with fiber optic backbones. In any case where the cam/security network will connect to the main network, the security provider should work closely with network administrators.
Where there are special considerations for power or data availability (e.g. real-time remote video feeds, video feeds for AI processing, or locks/alarms for sensitive sites), such use cases will need special consideration. In those cases, bandwidth and storage needs near each node should scoped carefully in cooperation with network administrators.
WiFi-first or WiFi-only networks are increasingly common in a variety of commercial environments (including offices, warehouses, and factories). At this time, we do not recommend connecting security systems via WiFi. Bandwidth concerns are especially acute for video data over wireless networks. If it must be done for operational reasons, we recommend a separate network (like a guest network) for security equipment. System administrators will need to pay special attention to securing that network and correctly configuring firewalls.
Mesh networks are uncommon, but it is not recommended to use security equipment as mesh nodes in most cases. In a mesh environment, we would recommend a separate trunk for the cam/security network off a mesh node as in a mid/large facility. Special attention will need to be paid to cybersecurity.
CONCLUSION
There are many reasons to prefer a separate “camnet” or security network to simply adding security devices to the main network, although this isn’t always practical from a cost or operations perspective. If a separate camnet is not feasible, power and data should be considered carefully – ideally in cooperation with network administrators – to ensure that both the main data network and security devices will function without disruption to the business’ operations.
If you need a security partner who can help guide you through these decisions or work closely with your IT team, please get in touch:
* “IDF” = “intermediary distribution facility” – colloquially, a secondary networking closet in addition to the primary server room or “MDF” (main distribution facility)